HALF-DISKLESS using ISHAREDISK ver 1.3
Isharedisk is a virtual disk software that enables client pc to have a virtual physical disk within its system.
This can work even on non gigabit networks although the read/write speed of your virtual disk will be hampered by limiting the maximum transfer speed of 100mb across client computers.
First download isharedisk ver 1.3 for 64 bit here
After you download install server isharedisk on your preferred location on your server.
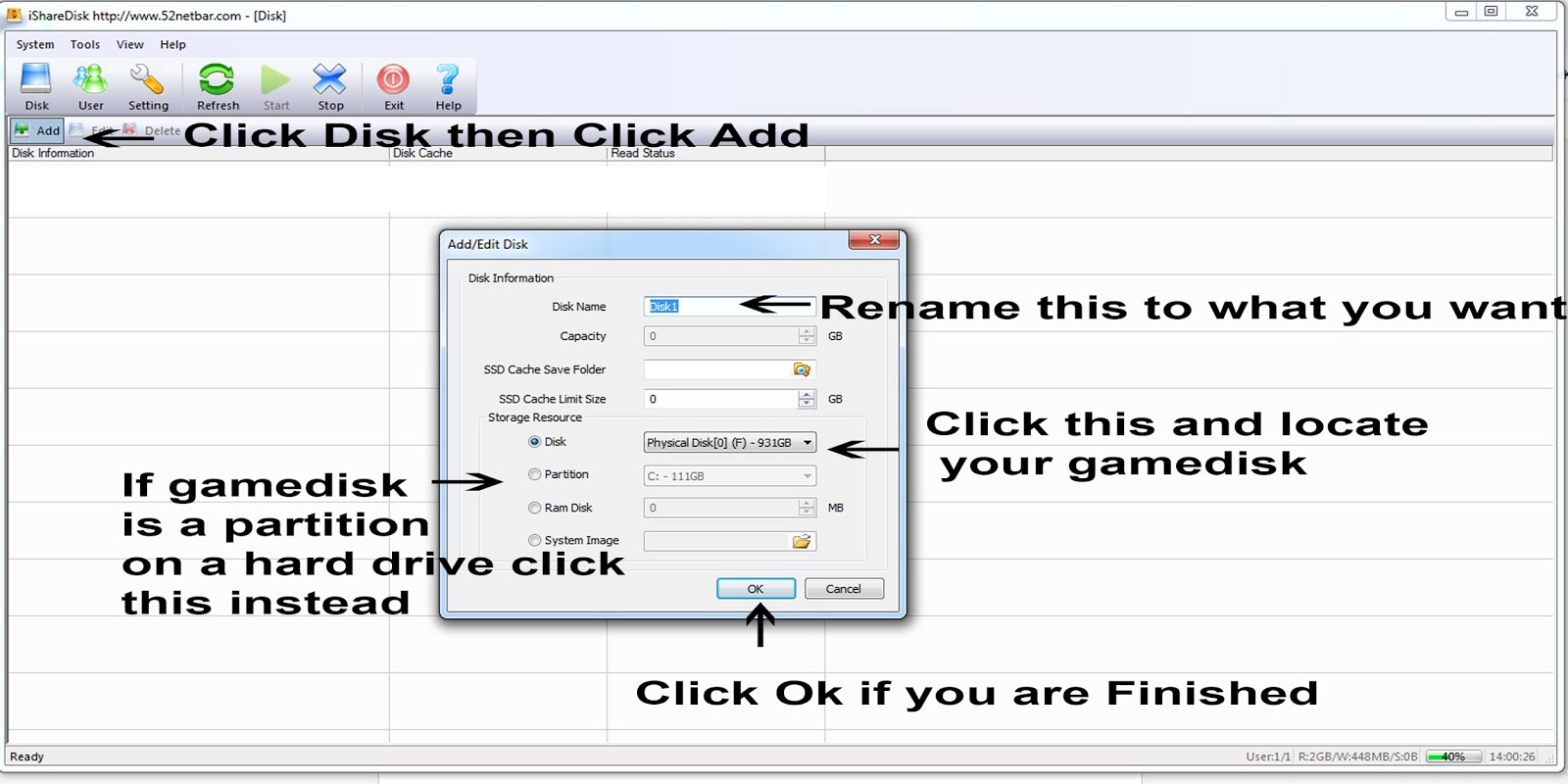
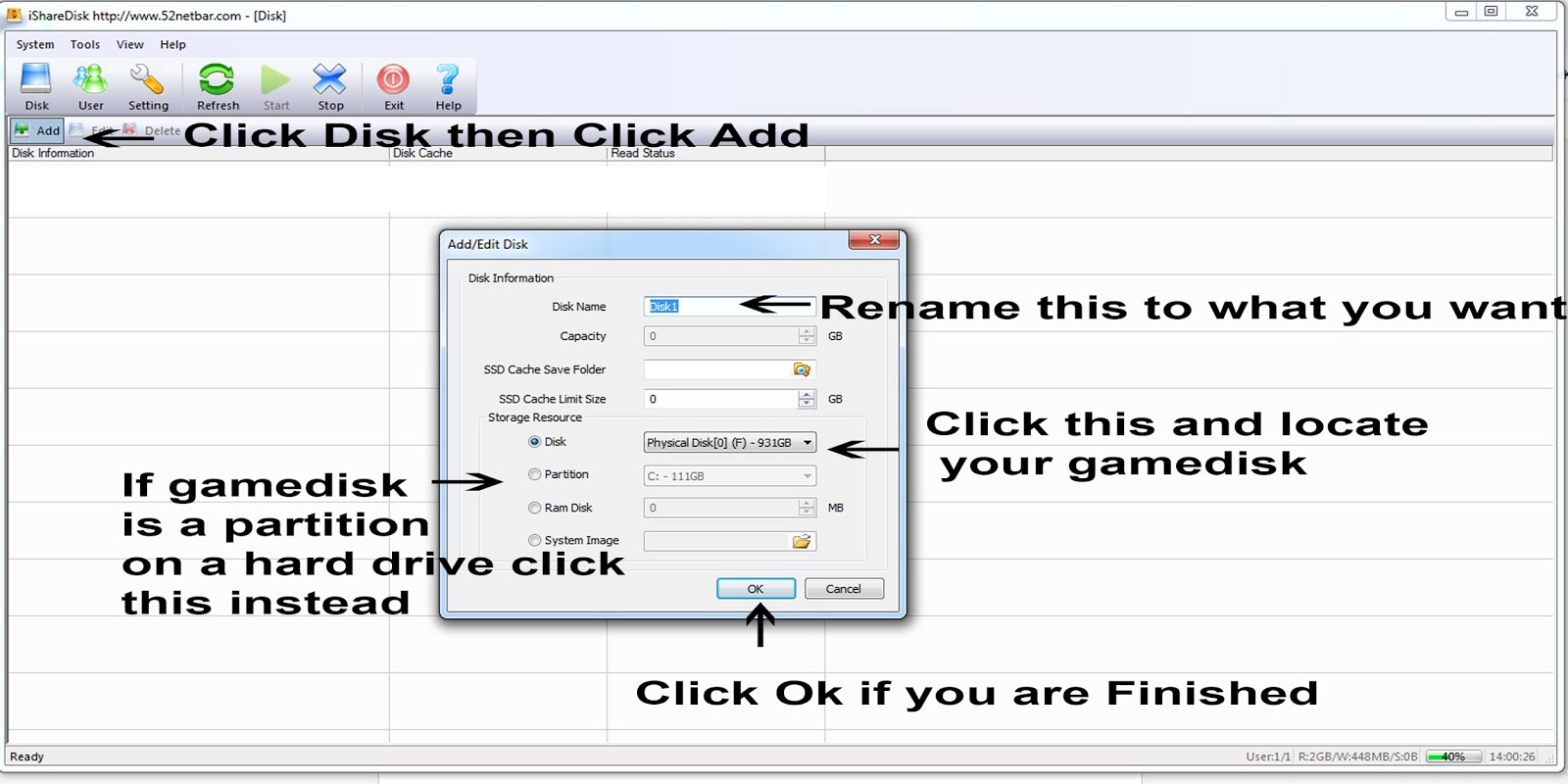
Next Open Isharedisk
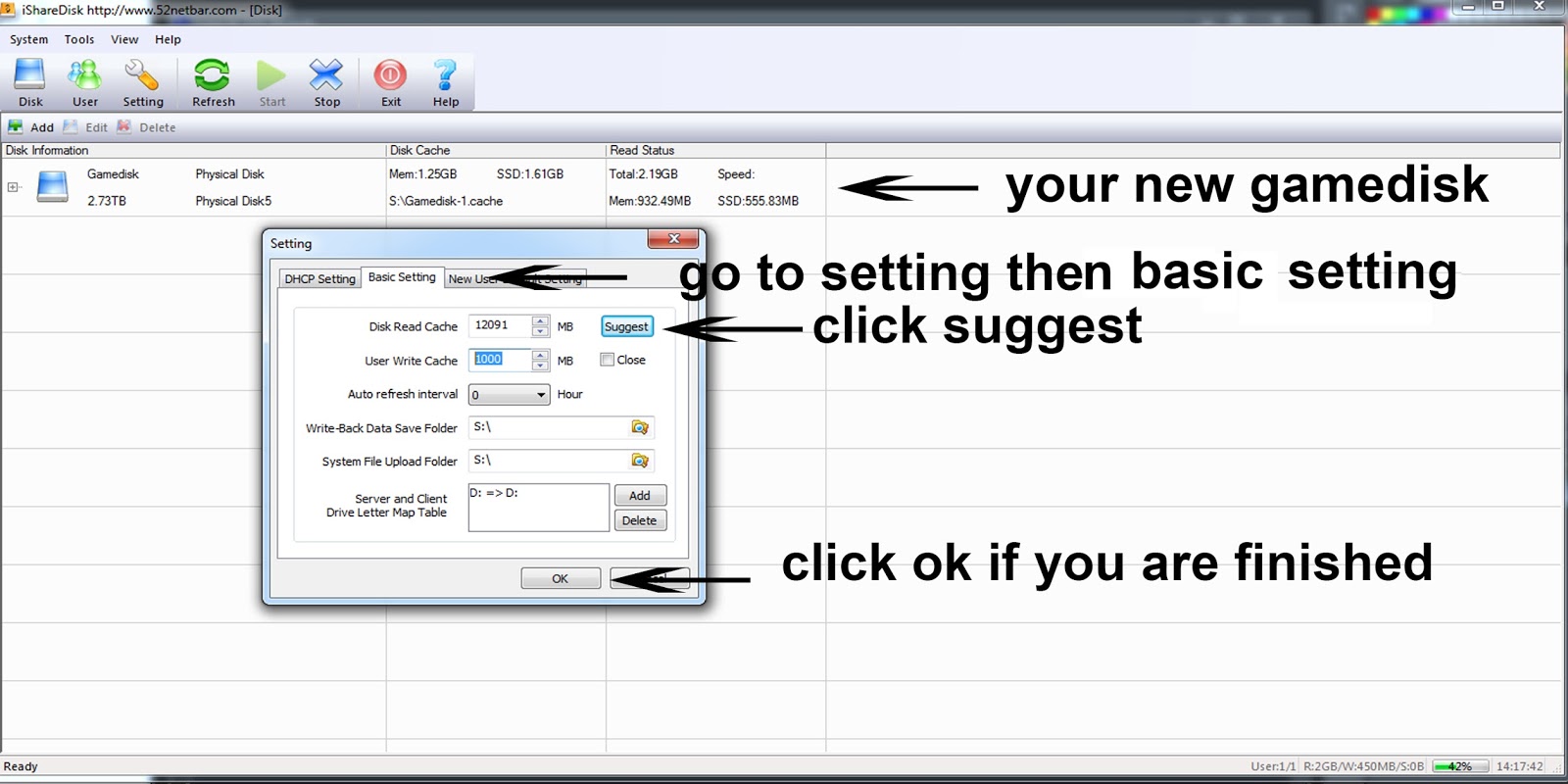
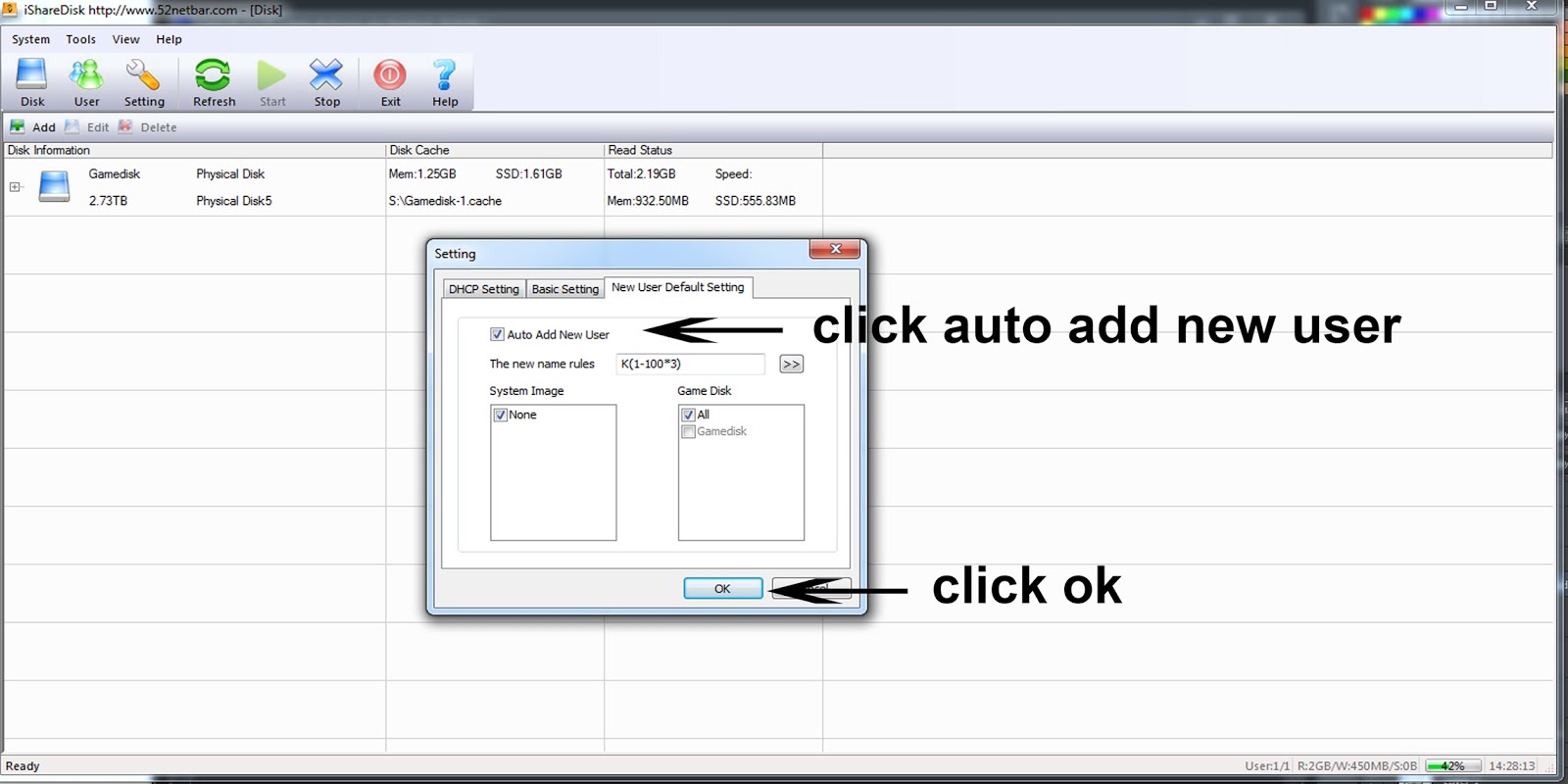
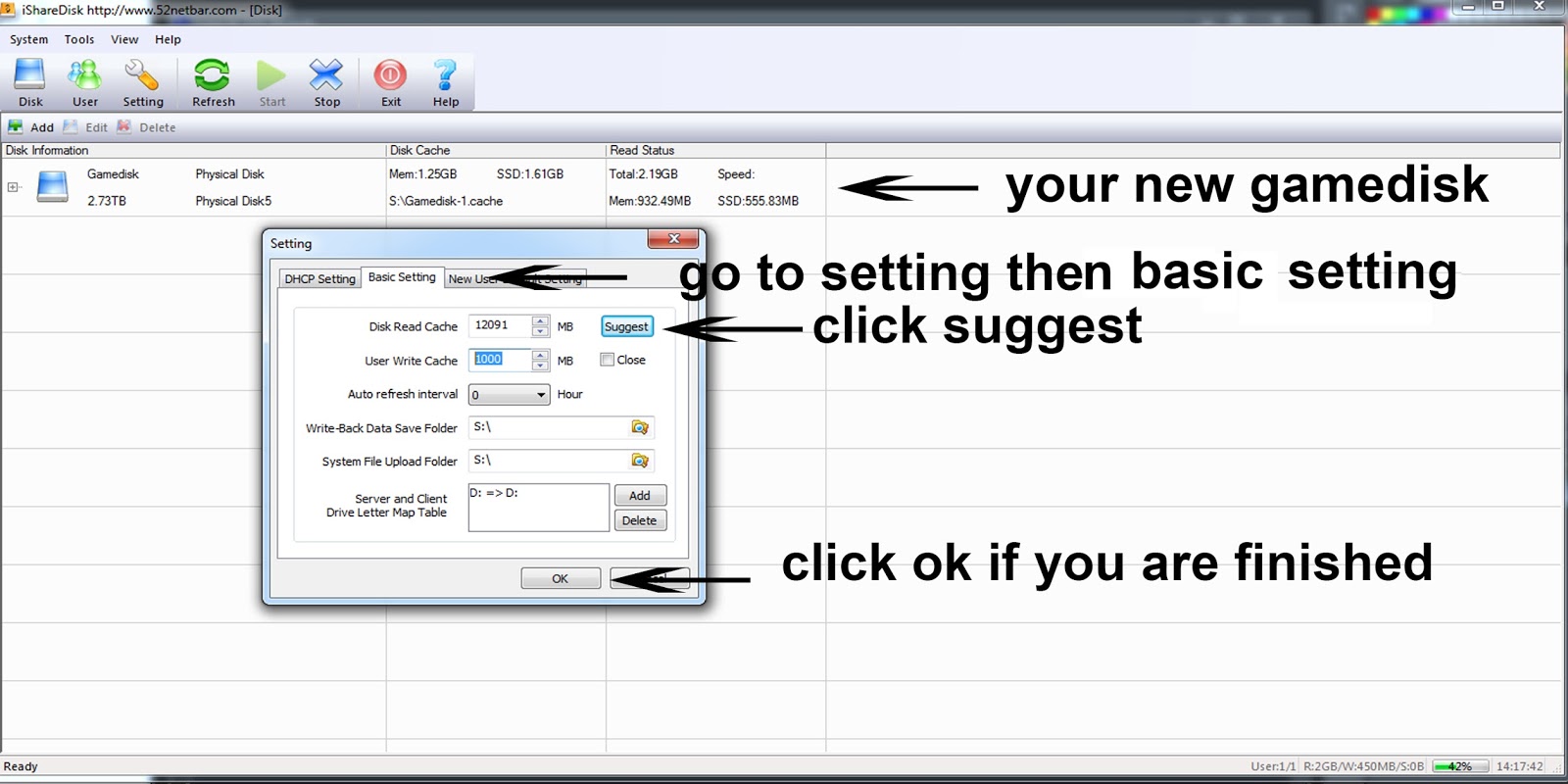
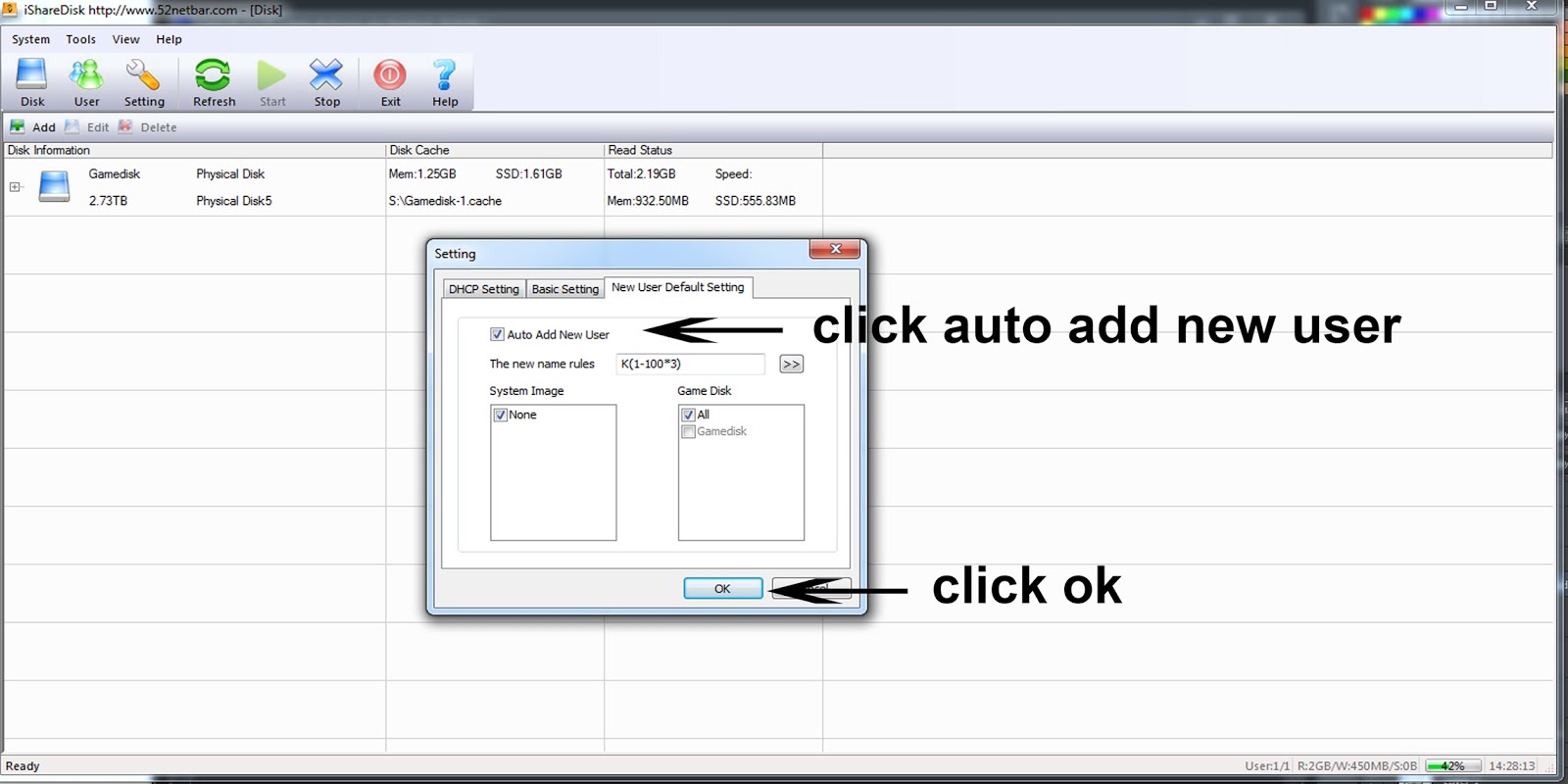
Then go to settings
Now you're ready to have your virtual disk in your client computer.
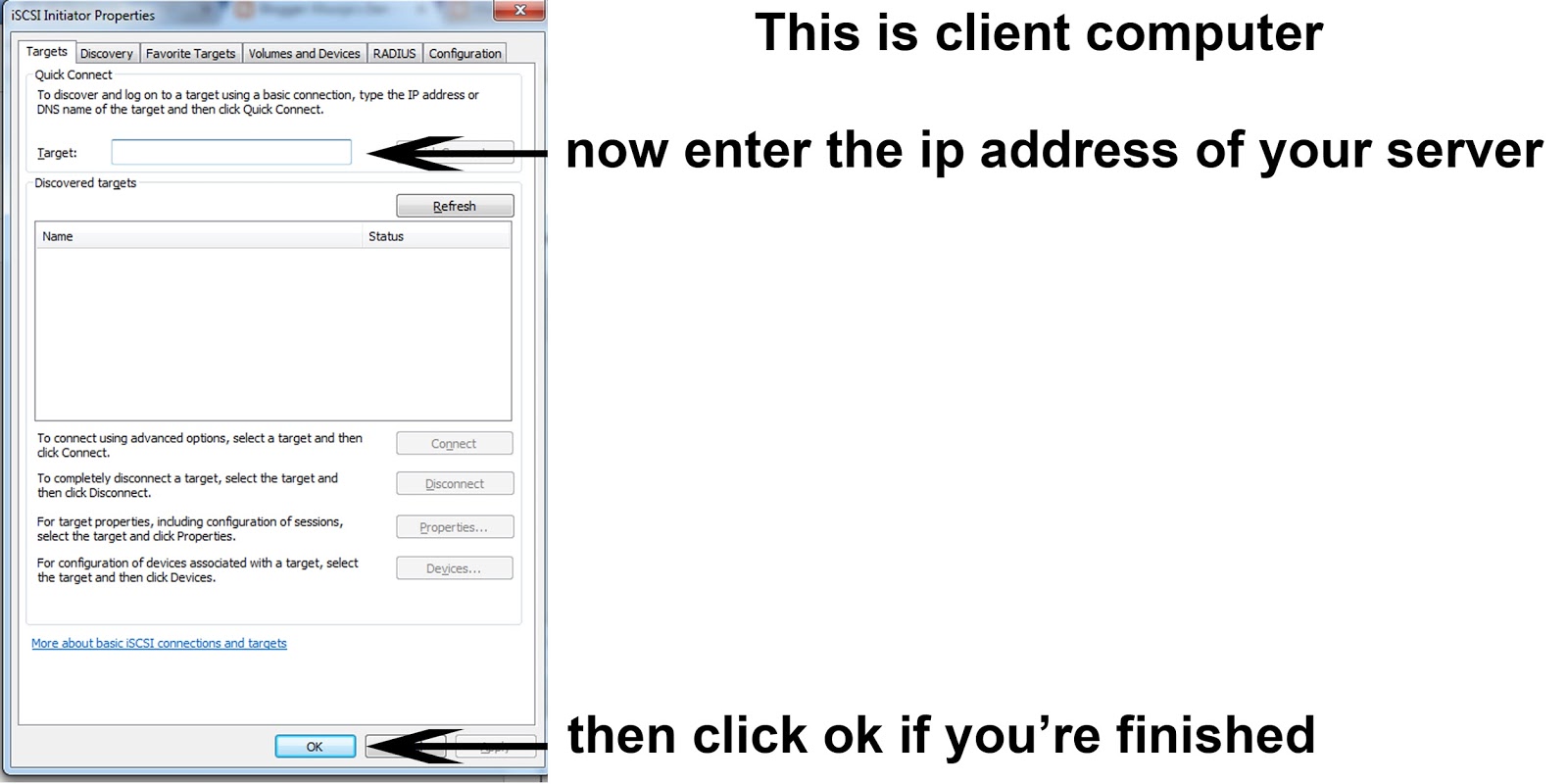
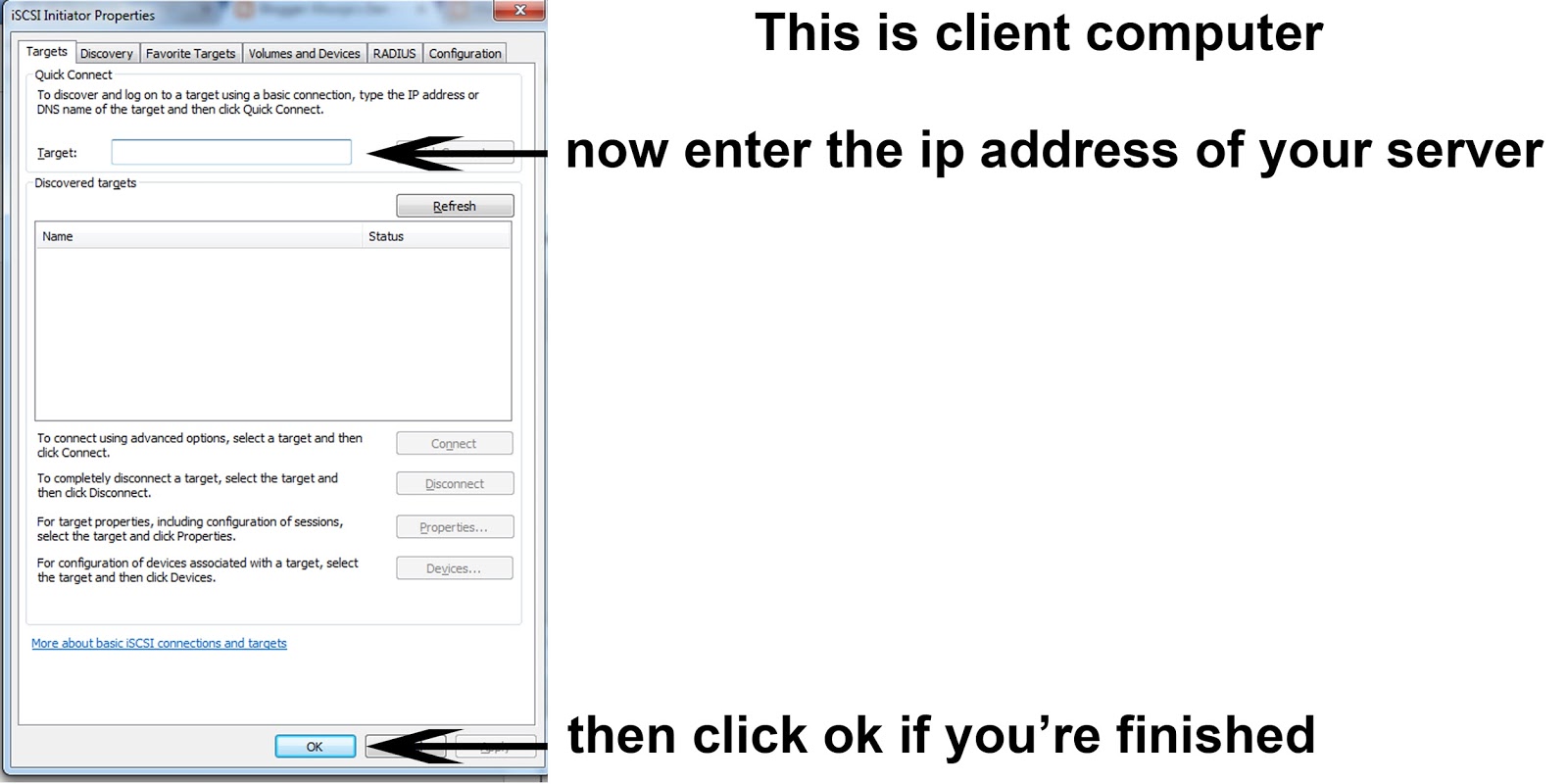
Go to your client computer then click Start then type ISCSI Initiator then click.
Now your new virtual game disk is ready.

This can work even on non gigabit networks although the read/write speed of your virtual disk will be hampered by limiting the maximum transfer speed of 100mb across client computers.
First download isharedisk ver 1.3 for 64 bit here
After you download install server isharedisk on your preferred location on your server.
Next Open Isharedisk
Then go to settings
Now you're ready to have your virtual disk in your client computer.
Go to your client computer then click Start then type ISCSI Initiator then click.
Now your new virtual game disk is ready.













